Zero Trust Architecture - A Practical Implementation Guide
A comprehensive guide to understanding and implementing Zero Trust security architecture in modern enterprise environments.
Read More →Cybersecurity articles, tutorials, and insights from my experience in SOC operations and penetration testing.
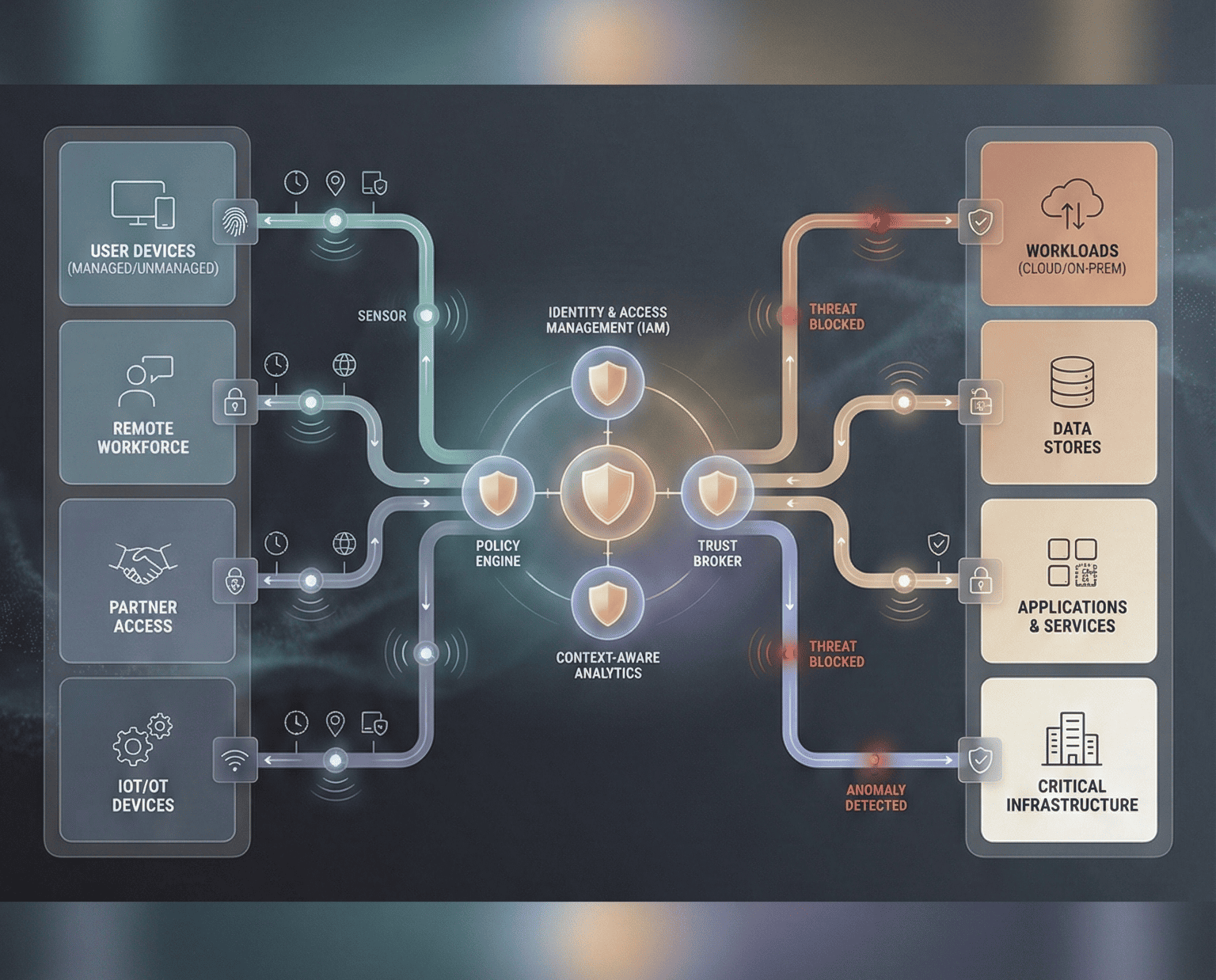
A comprehensive guide to understanding and implementing Zero Trust security architecture in modern enterprise environments.
Read More →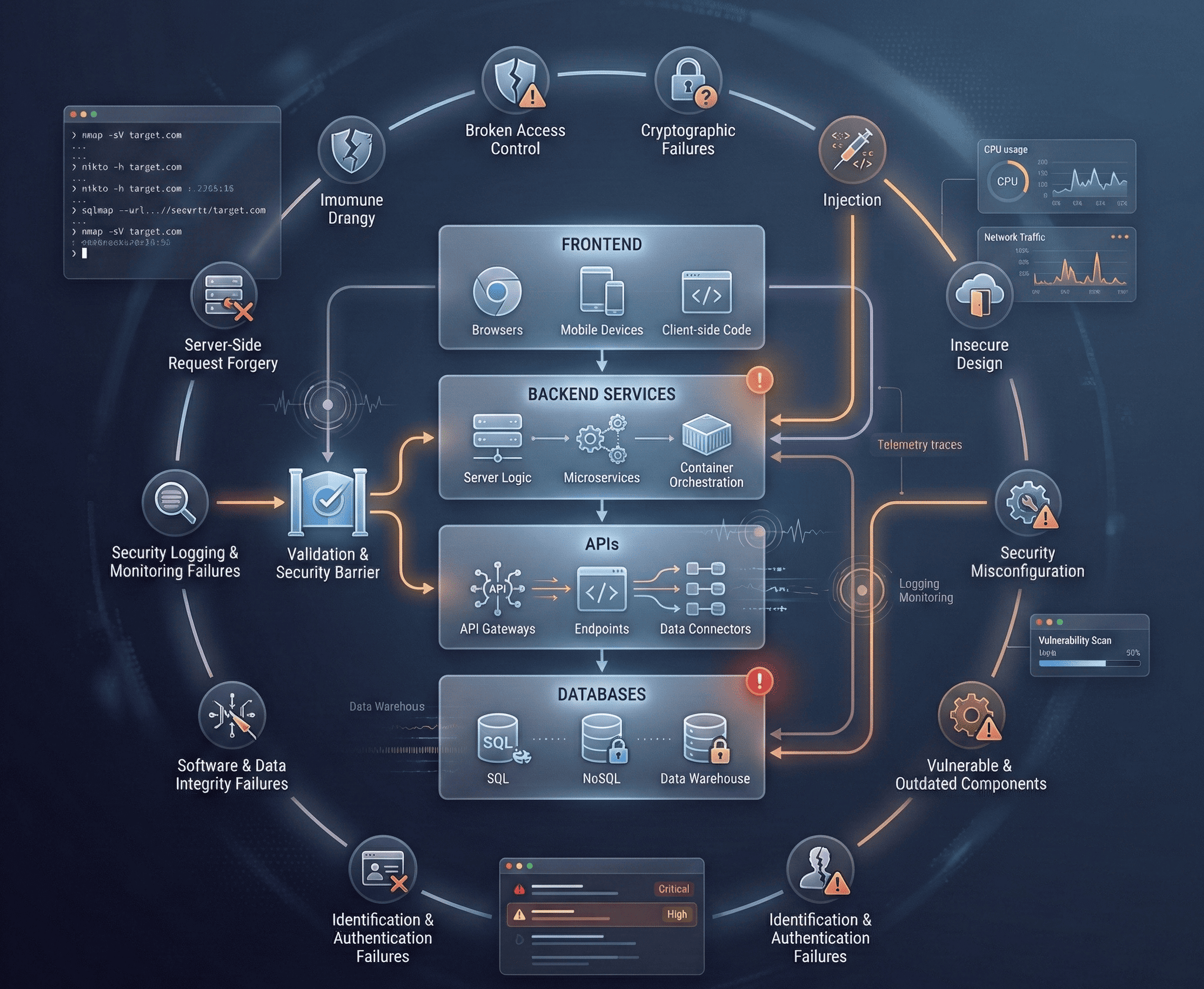
Deep dive into modern web application security testing techniques, OWASP Top 10 exploitation, and professional pentesting methodology.
Read More →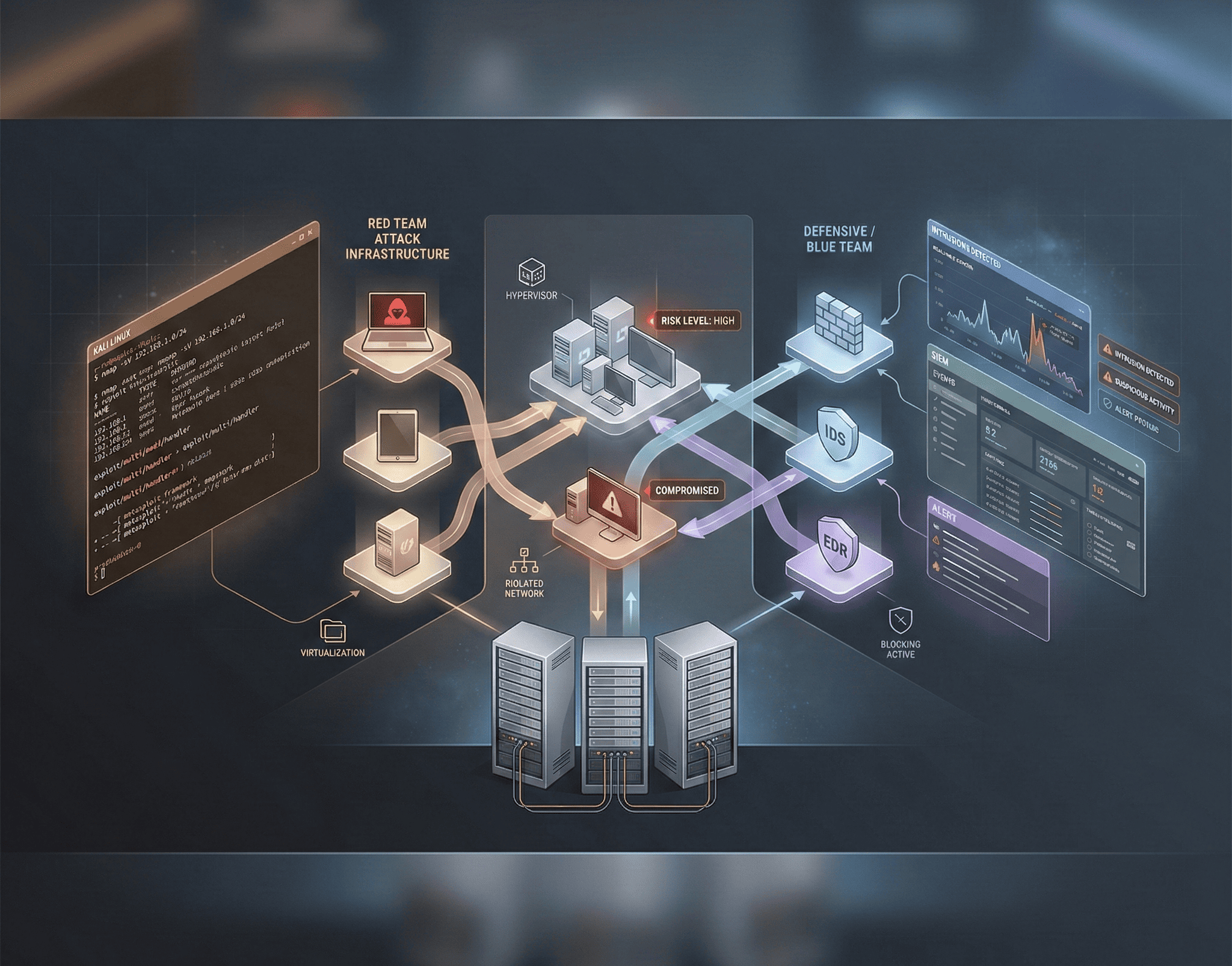
Step-by-step guide to building your own penetration testing and red team lab environment for security practice and skill development.
Read More →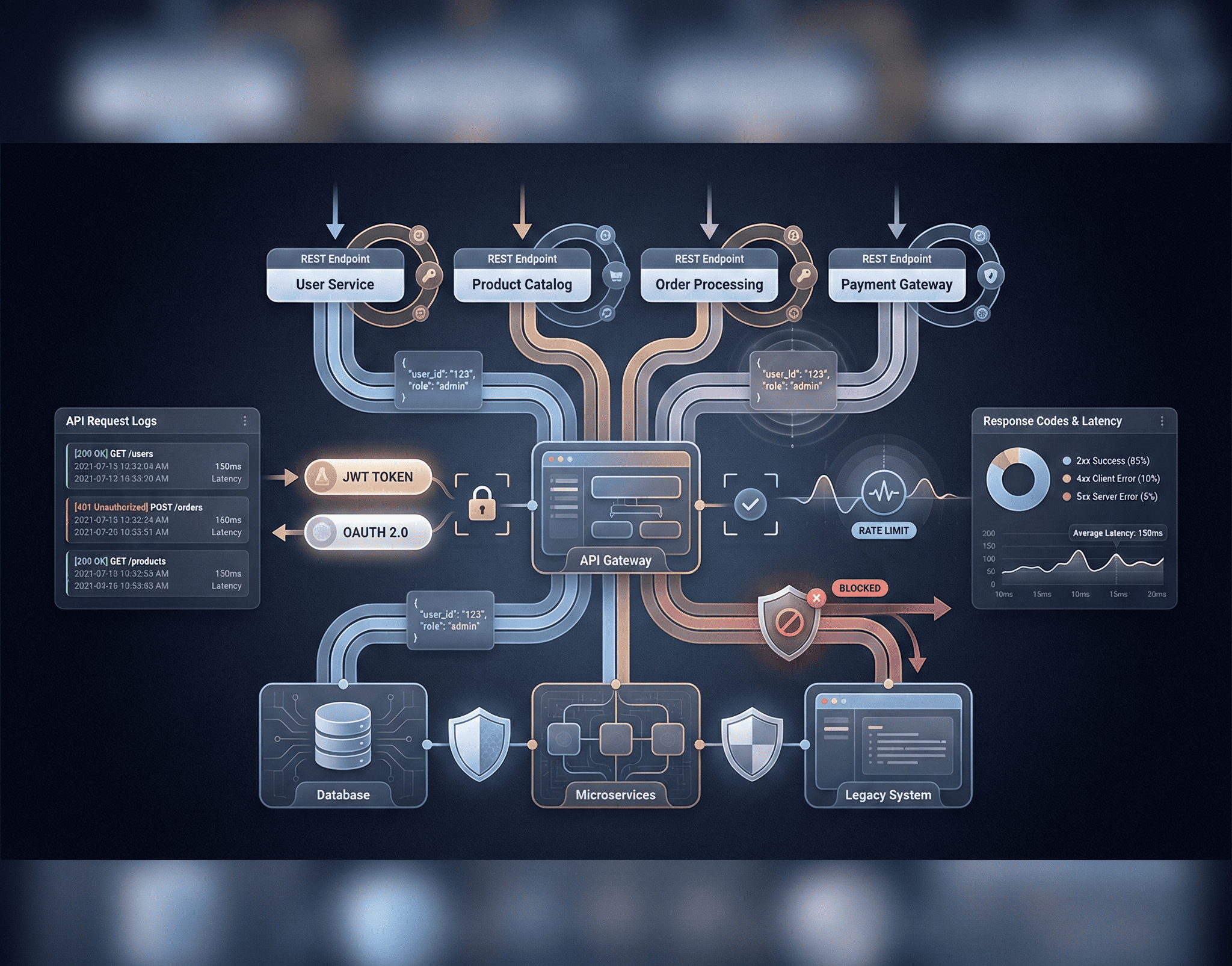
Comprehensive guide to API security testing, covering REST, GraphQL, authentication bypass, and common API vulnerabilities.
Read More →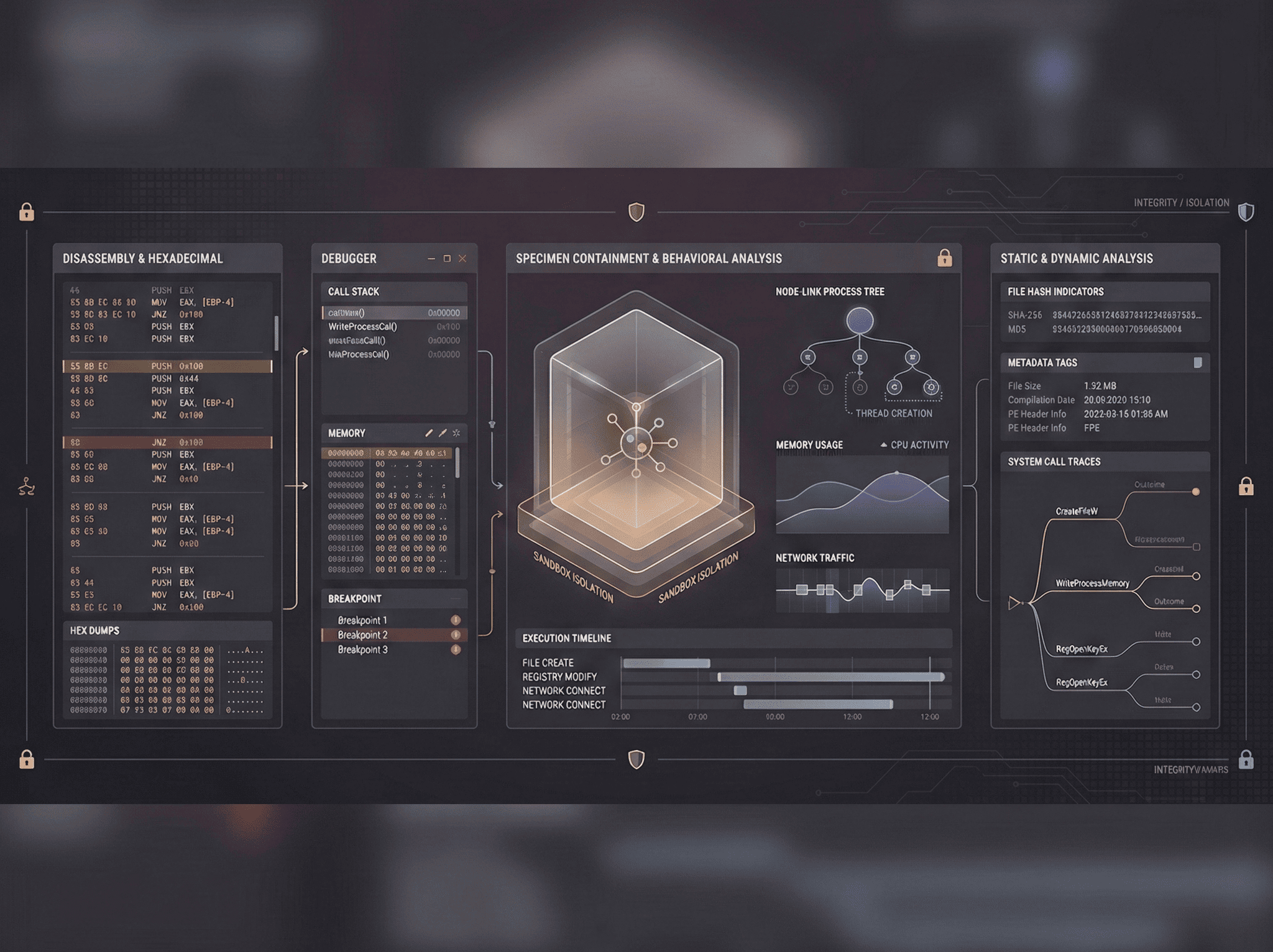
Introduction to malware analysis techniques including static analysis, dynamic analysis, behavioral analysis, and practical case studies.
Read More →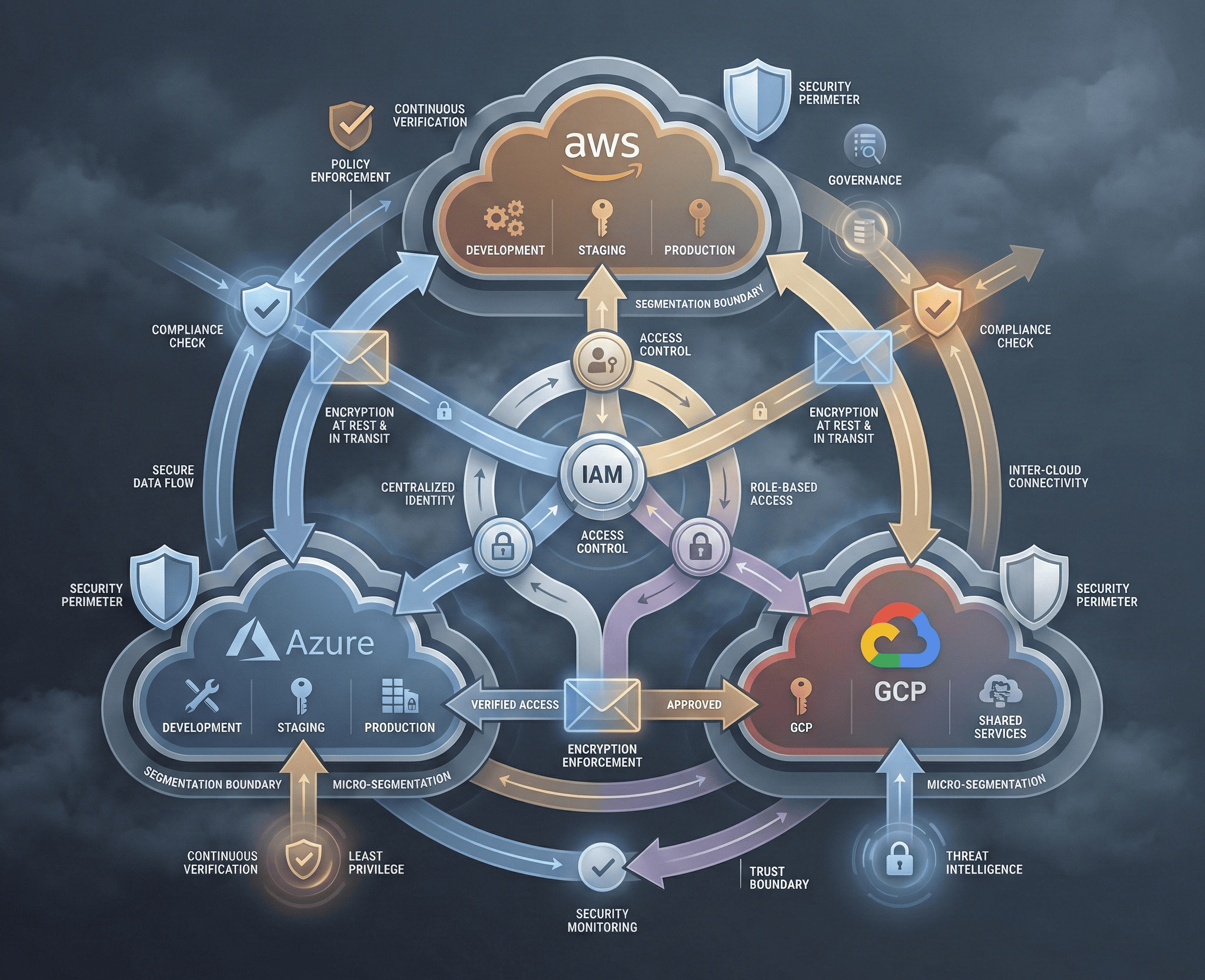
Comprehensive guide to cloud security best practices across AWS, Azure, and GCP, covering IAM, misconfigurations, and multi-cloud security strategies.
Read More →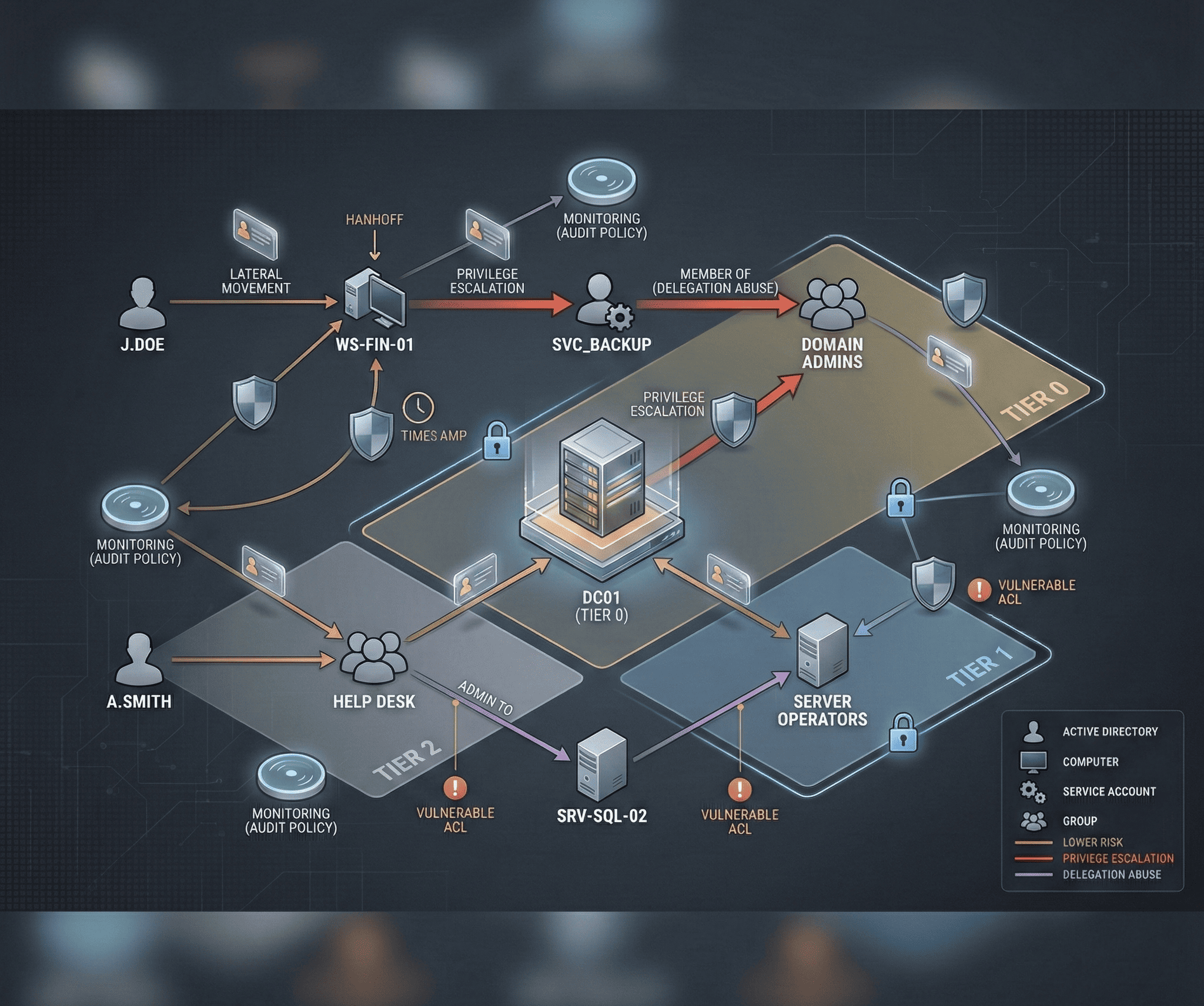
In-depth guide to Active Directory attack techniques and defense strategies, covering enumeration, lateral movement, persistence, and detection.
Read More →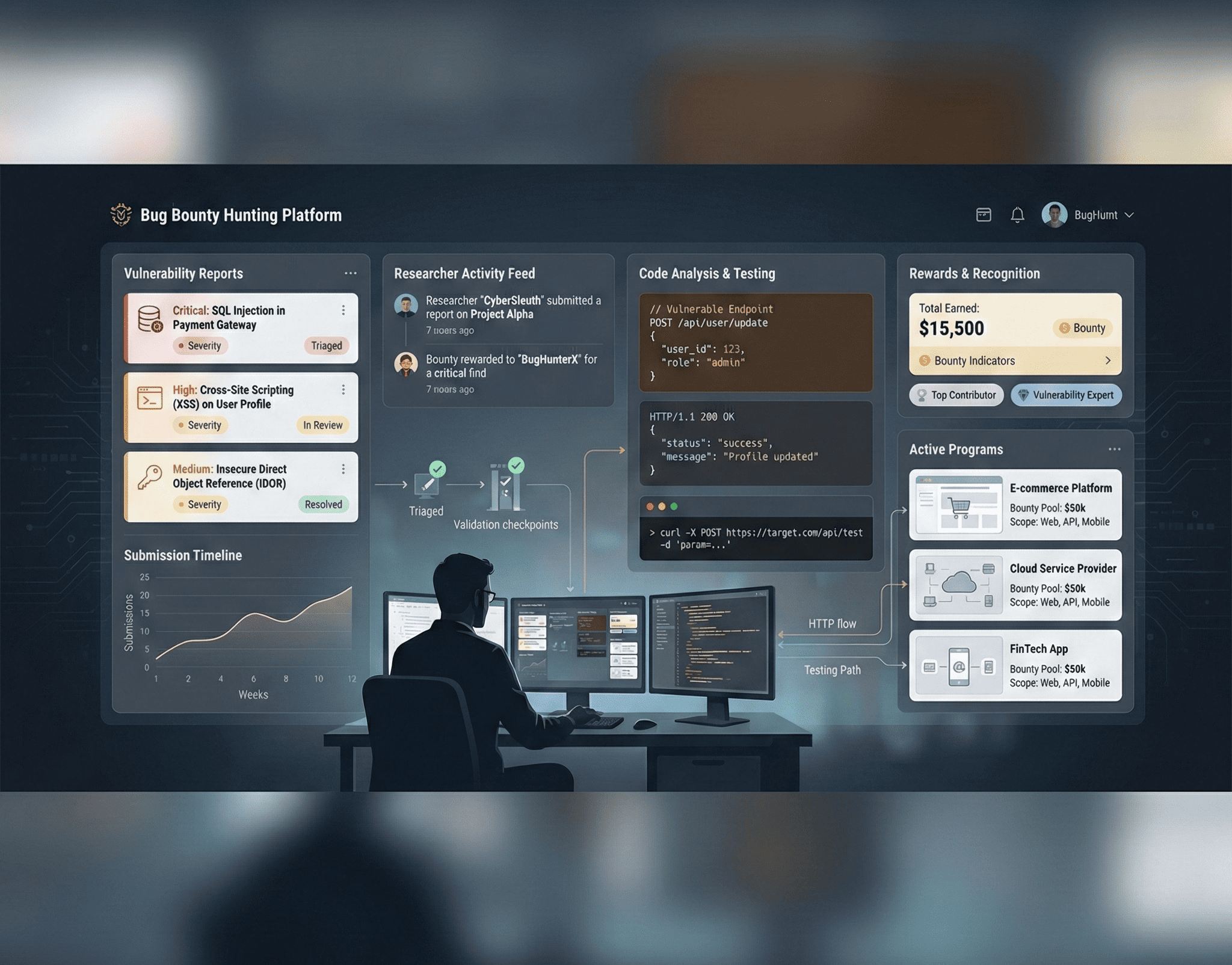
Complete guide to starting your bug bounty hunting journey, from choosing platforms to writing reports and earning your first bounty.
Read More →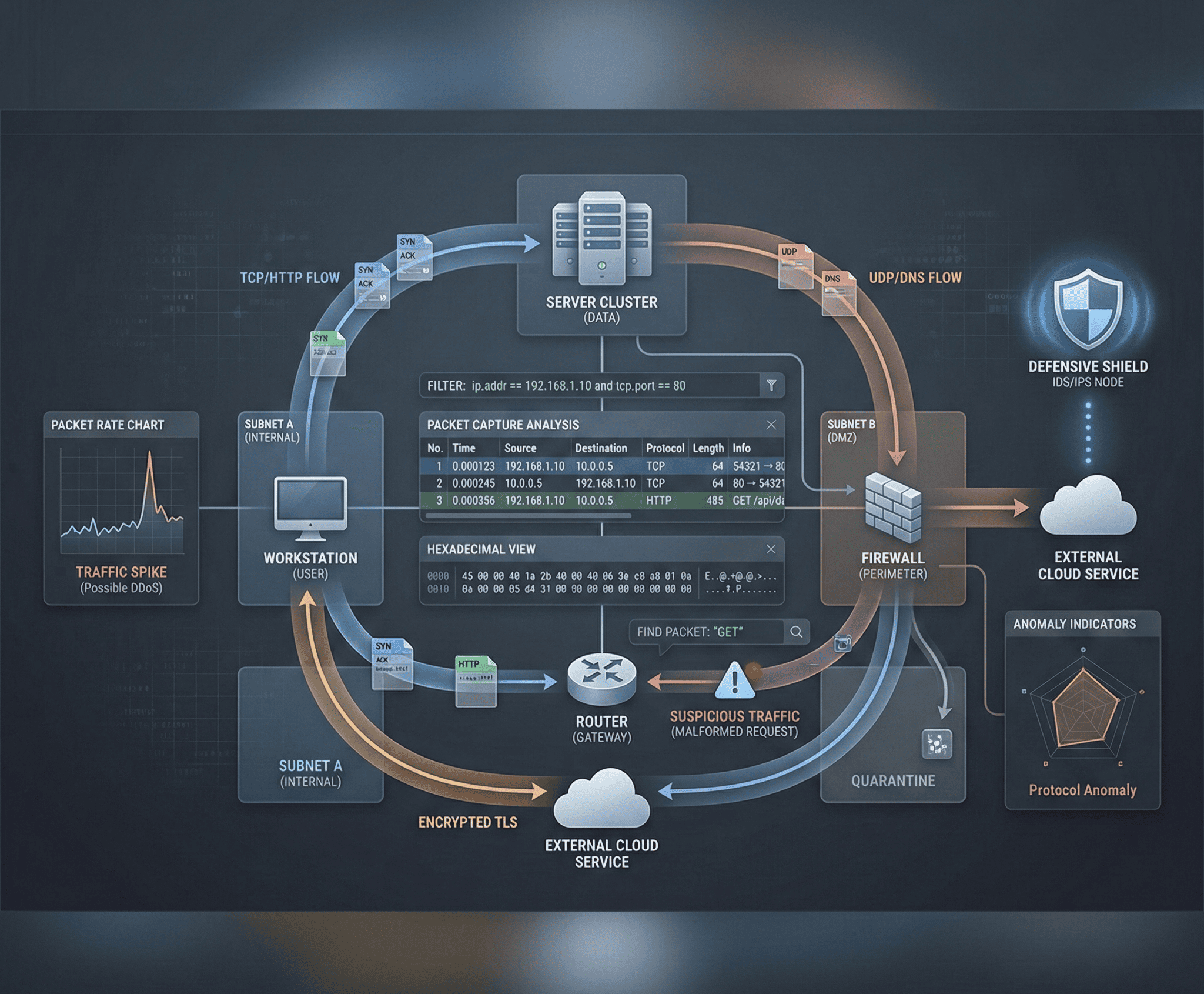
Practical guide to network security monitoring using Wireshark and Zeek for traffic analysis, threat hunting, and incident detection.
Read More →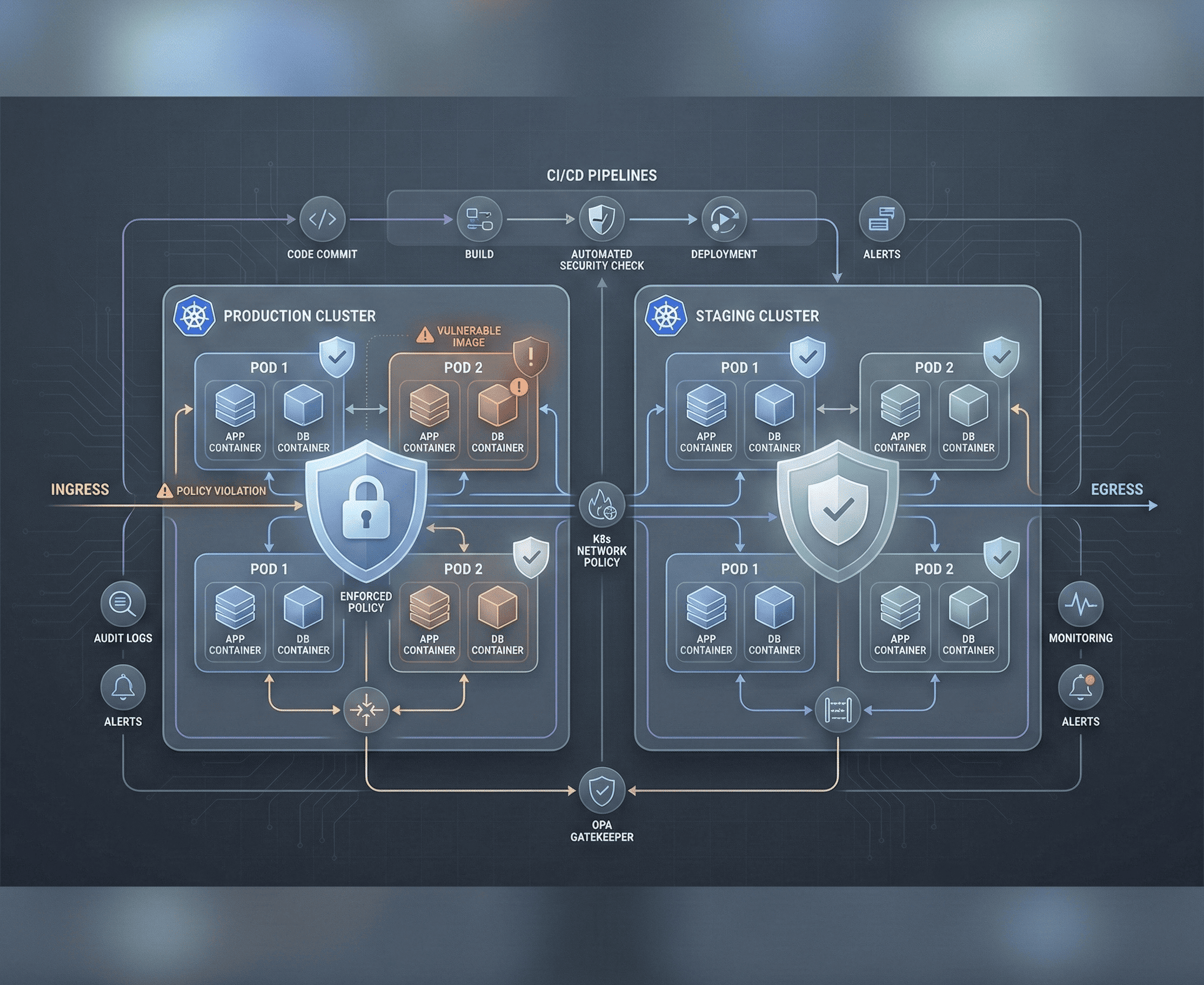
Advanced guide to securing Docker containers and Kubernetes clusters, covering image scanning, RBAC, runtime security, and incident response.
Read More →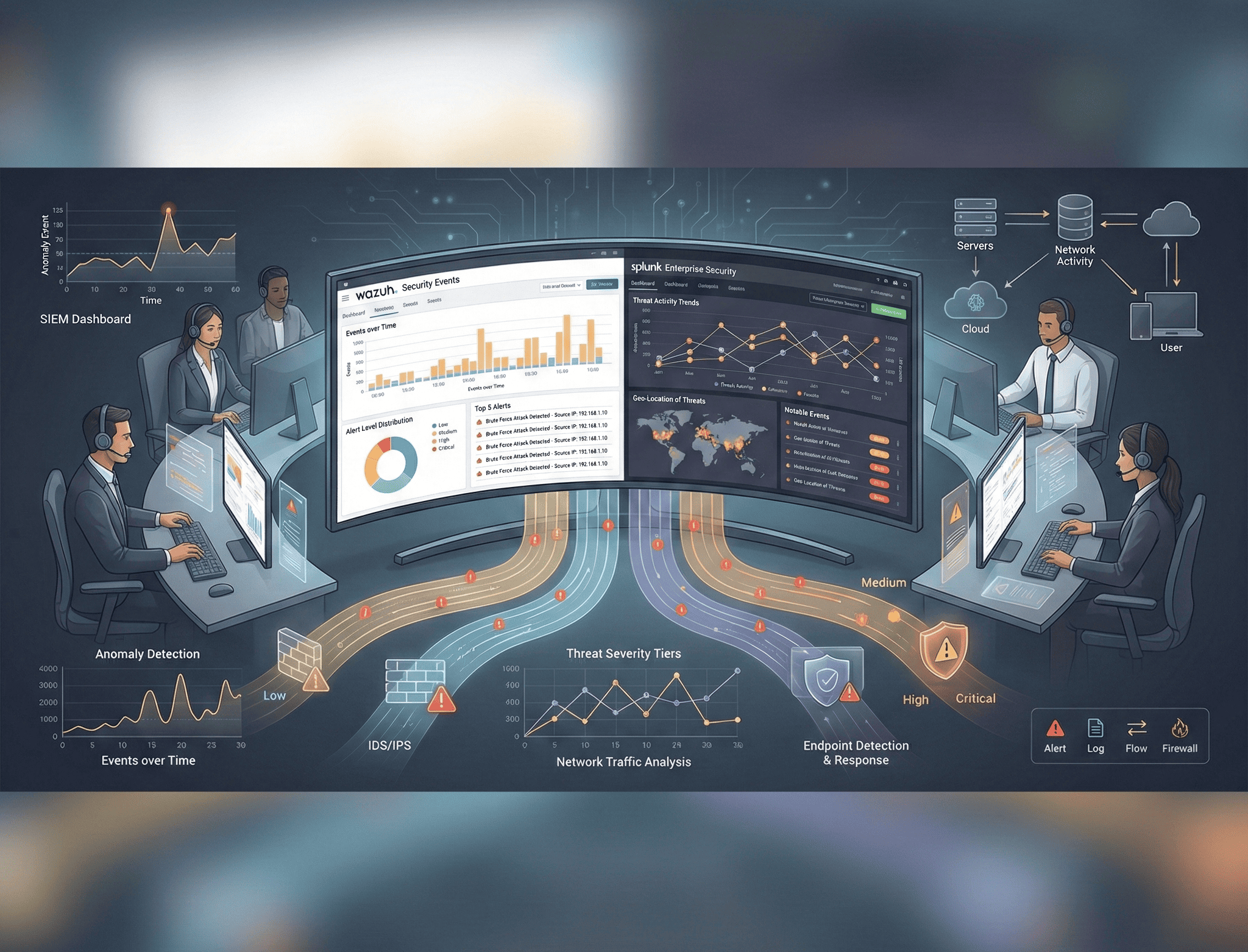
Practical guide to deploying SIEM solutions using Wazuh and Splunk for threat detection, custom rules, and incident response workflows.
Read More →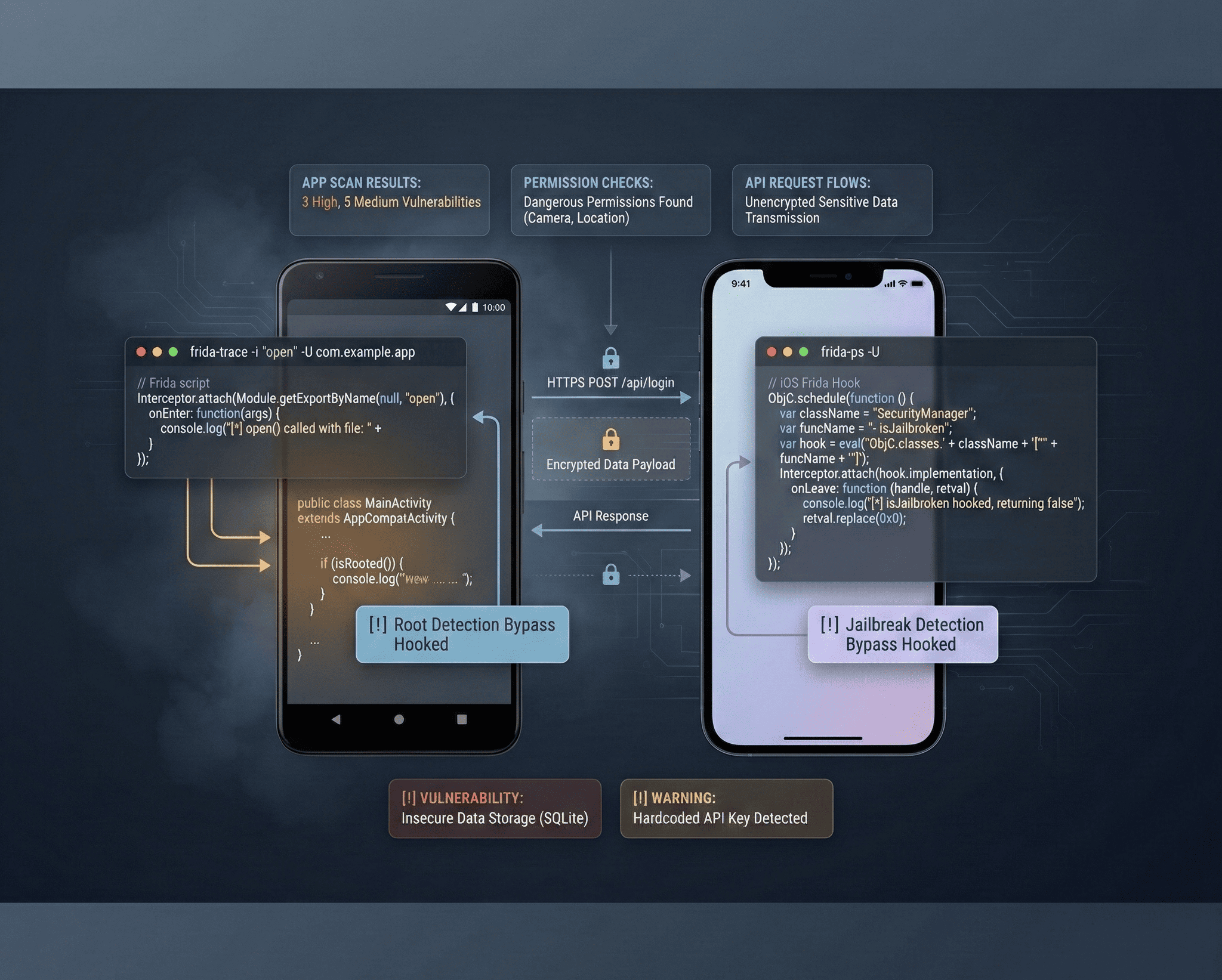
Comprehensive guide to mobile application security testing for Android and iOS, covering static analysis, dynamic analysis, and reverse engineering.
Read More →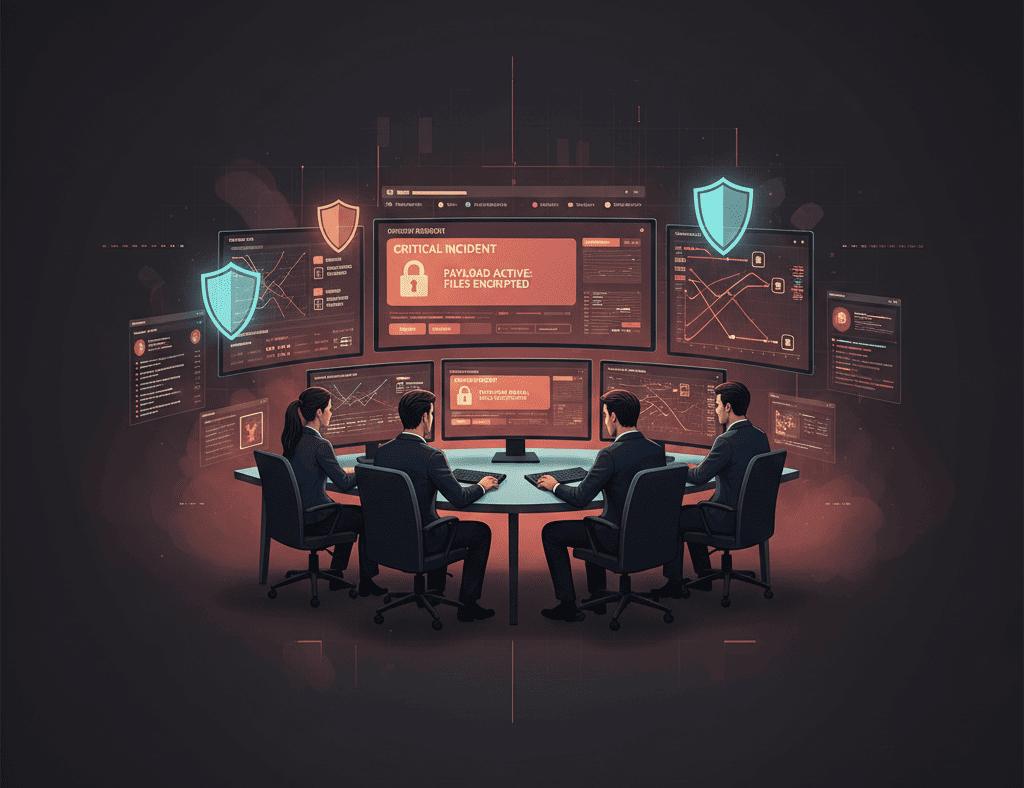
Step-by-step incident response playbook for handling ransomware attacks, covering detection, containment, eradication, recovery, and forensic analysis.
Read More →
Guide to secure code review methodology, common vulnerability patterns across languages, and automated SAST tools for application security.
Read More →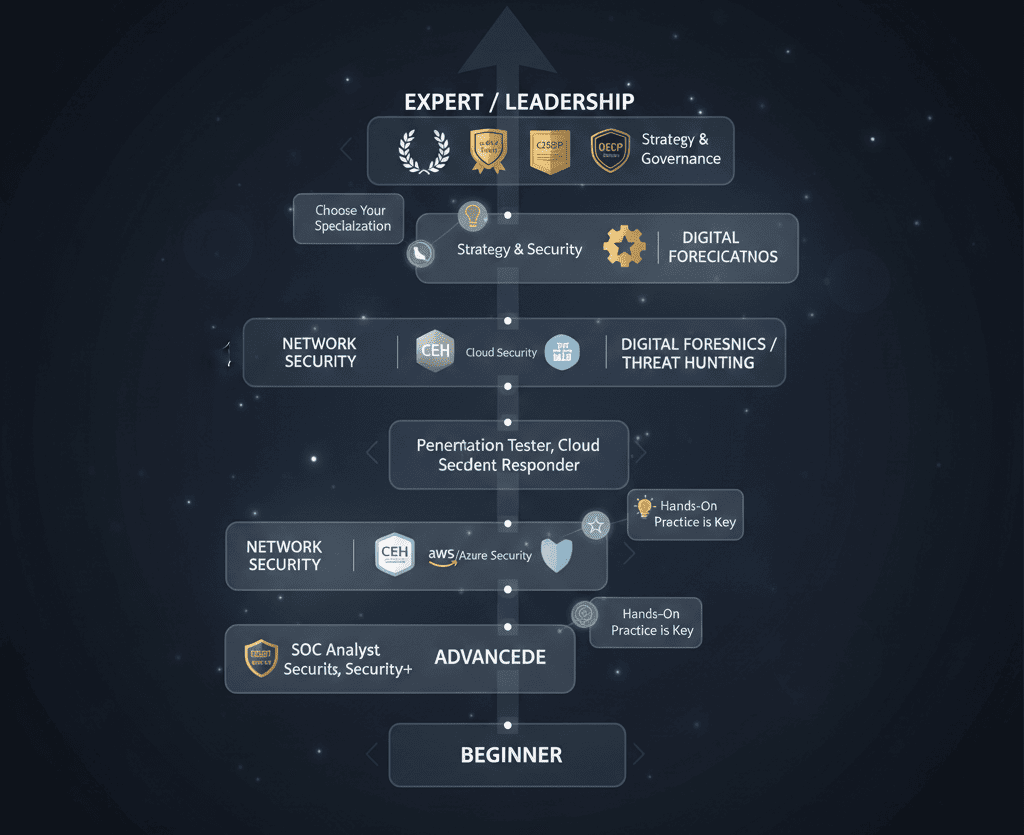
Personal guide to building a successful cybersecurity career, covering learning paths, certifications, portfolio building, and job search strategies.
Read More →
Complete guide to setting up enterprise-grade SIEM at home for threat detection and analysis practice.
Read More →Sharing my learning journey, favorite CTF rooms, and techniques that helped me reach top 4% globally.
Read More →Real-world application of ATT&CK tactics in threat hunting and SIEM rule creation based on SOC experience.
Read More →